CVE-2026-31431 copyfail mitigation
Recently Xint disclosed a very critical vulnerability in the Linux kernel, CVE-2026-31431, which allows local attackers to gain root privileges. More details about how this vulnerability works can be found in the Xint Blogpost.
We provide a demo that you can use in order to test if your system is vulnerable to this issue.
Do not use this code on systems you do not own or explicitly have permission to test.
Be careful to backup your original su binary as this exploit modifies it.
Testing
On a local machine
First, ensure bakup the su binary on your system, as this exploit may modify it:
root# cp /usr/bin/su /usr/bin/su.bak
Then with a non-root user, run the following commands to execute the exploit script:
user$ curl https://gitlab.cwcloud.tech/oss/cve-2026-31431-demo/-/raw/main/cve-2026-31431.py > cve-2026-31431.py
user$ python3 cve-2026-31431.py
root#
Then restore the original su binary:
root# mv /usr/bin/su.bak /usr/bin/su
With docker compose
Better with safer isolation (not contaminating your su binary):
$ git clone https://gitlab.cwcloud.tech/oss/cve-2026-31431-demo.git
$ cd cve-2026-31431-demo
$ docker compose up -d --build --force-recreate
$ docker exec -it cve-2026-31431 /bin/bash
demo@8536b73279be:/app$ su -
#
Mitigation
Xint has provided a way to mitigate for several distributions including Debian or Ubuntu:
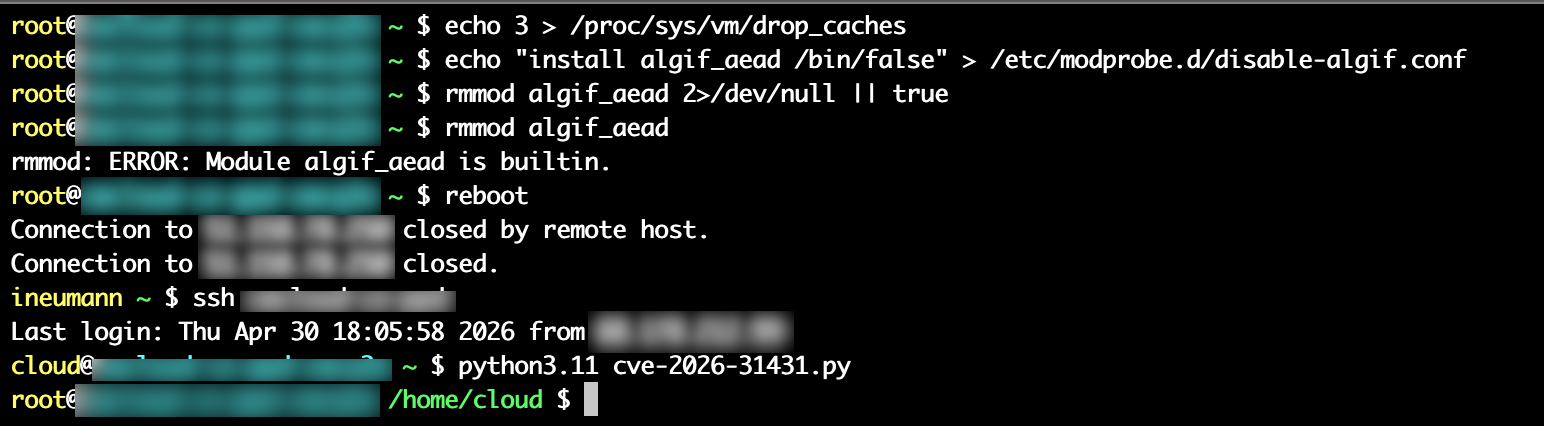
root# echo 3 > /proc/sys/vm/drop_caches
root# echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif-aead.conf
root# rmmod algif_aead 2>/dev/null || true
But due to the 2>/dev/null || true, lot's of people aren't aware that the mitigation is not working on all distributions, and in particular on RHEL based distributions and miss the following error message:
rmmod: ERROR: Module algif_aead module is bultin.
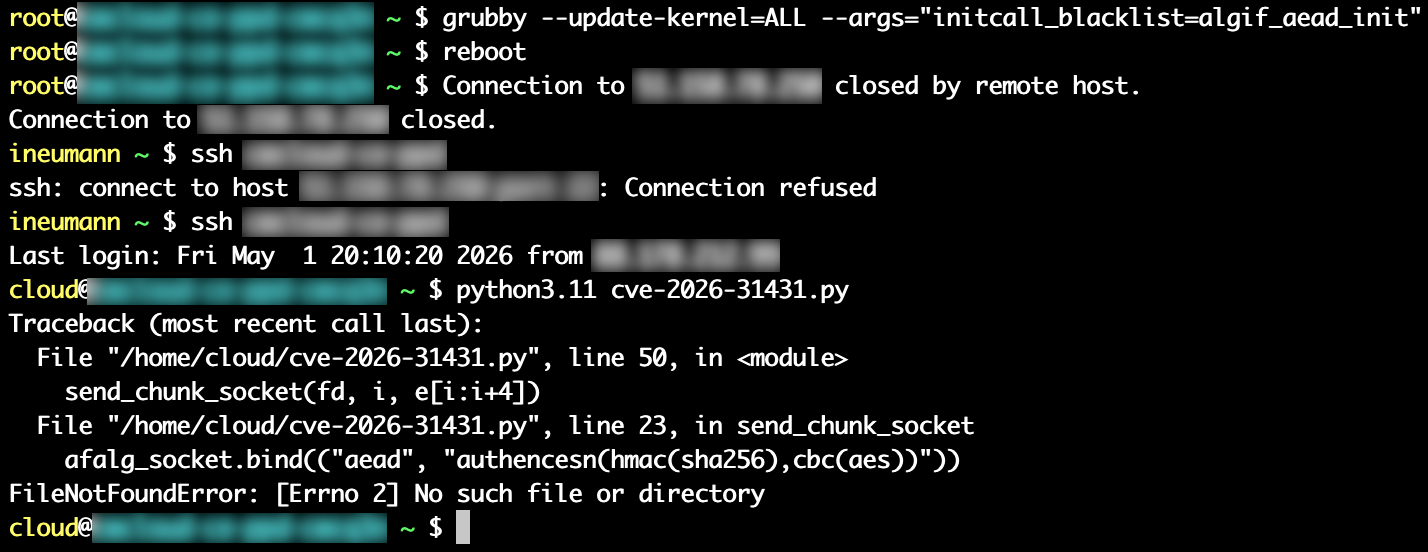
Here's a demo which shows the mitigation ain't working on Almalinux:
And unfortunately, all the mitigations for those distributions involve a reboot. Here's one of the simplest until a new kernel patch is released:
root# grubby --update-kernel=ALL --args="initcall_blacklist=algif_aead_init"
root# reboot
Here's a demo of the mitigation working on the same Almalinux system (after restoring the original su binary):